Newsroom

2026 Cybersecurity: Securing Cookie Consent and Analytics Infrastructure
30 April 2026
The Psychology of a Hacker or How to Detect the Early Warning Signs
01 December 2025
How to build a threat model
11 November 2025
How Drones, IIoT, and Cybersecurity Are Redefining Modern Warfare
24 October 2025

Avoiding EU “Chat Control” and Chat Surveillance
14 October 2025
Browse by topic

AI-Driven Supply Chain Attacks: The New Frontier of Cybersecurity Risk
17 April 2026
supply-chain-securityai-threatsrisk-management
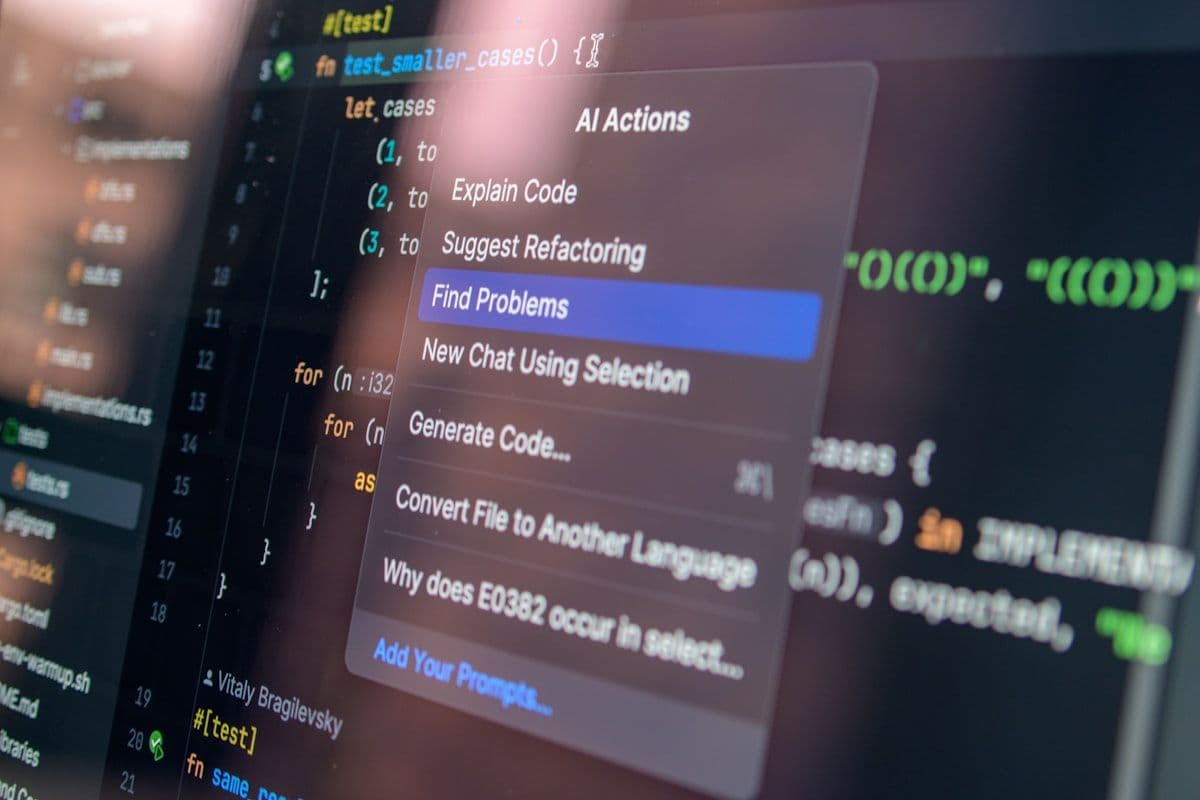
Why AI Code Audits Fall Short: The Limits of Automated Security Reviews
14 April 2026
code-auditAI-securityvulnerability-assessment
Blockchain Evolution: Strengthening Enterprise Security in 2026
11 April 2026
blockchainfinancial-securityenterprise-security
The Evolved CISO: Moving Beyond Traditional Security to Strategic Leadership
10 April 2026
CISOsecurity leadershipcybersecurity strategy

Critical Infrastructure at Risk: Analyzing Iran-Israel Cyber Conflict Targets
08 April 2026
nation-state-attackscritical-infrastructurecyber-warfare

The AI Replacement Trap: Why Your Best Cybersecurity Engineers Are Irreplaceable
07 April 2026
AIcybersecurityworkforcethreat-detectionincident-response

Stuxnet: The Digital Weapon That Changed Cybersecurity Forever
06 April 2026
stuxnetcritical-infrastructurenation-state-threats
2026 Cybersecurity Posture: Essential Updates for Modern Defense
06 April 2026
cybersecurityNISTcompliancezero-trustrisk-management
Q3 2025 in review: deepfakes, identity abuse, and the new shape of cybercrime
05 October 2025
Quarterly Review
Cyber resilience lessons from recent attacks
29 September 2025
IncidentManagement

Cyberattack Disrupts Major European Airports: What Happened and How to Respond
22 September 2025
CybersecurityVulnerability

The new iPhone 17 and why we need (more than ever) a Secure and Independent Mobile OS
12 September 2025
Mobile